Material Weaknesses
Let's dive into the internal control challenges faced by U.S. public cryptocurrency mining companies and explore practices to help you prevent similar issues.
Today, I wanted to take a look at issues in internal controls over financial reporting (ICOFR) of US public crypto mining companies identified in their recent filings, classify deficiencies identified, determine the most common causes of material weaknesses (MWs), and assess the measures that companies take to address the related issues.
We reviewed SEC filings of 29 issuers with material revenue from cryptocurrency mining operations and found 15 filings with identified MWs in internal controls. This means that 55% of the entities we reviewed had material weaknesses. For additional context, we compared this rate to the KPMG study of material weaknesses identified by public entities in the U.S. in 2023. We found that 242 out of 3,549 (7%) filers had MWs in 2023. Out of these 242 MWs, 16 were bitcoin mining companies1. This means that, although Bitcoin miners comprised just 0.8% of the total population, they were responsible for 6.6% of all material weaknesses in 2023.
Causes
As per the Committee of Sponsoring Organizations of the Treadway Commission (the organization that published the most widespread internal control framework adopted by the absolute majority of the U.S. public companies):
“For most public blockchains, users may not be able to obtain an understanding of the general IT controls implemented and the effectiveness of these controls. Furthermore, where there is no central authority to administer and enforce protocol amendments, there could be a challenge to establishing development/maintenance process control activities for the technology.”2
In other words, unless Bitcoin Core will start providing SOC reports or audit firms perform tests of internal controls over Bitcoin Improvement Proposal process, it is reasonable to expect MWs in the filings of all bitcoin miners. However, none of the filings we researched addressed this specific concern.
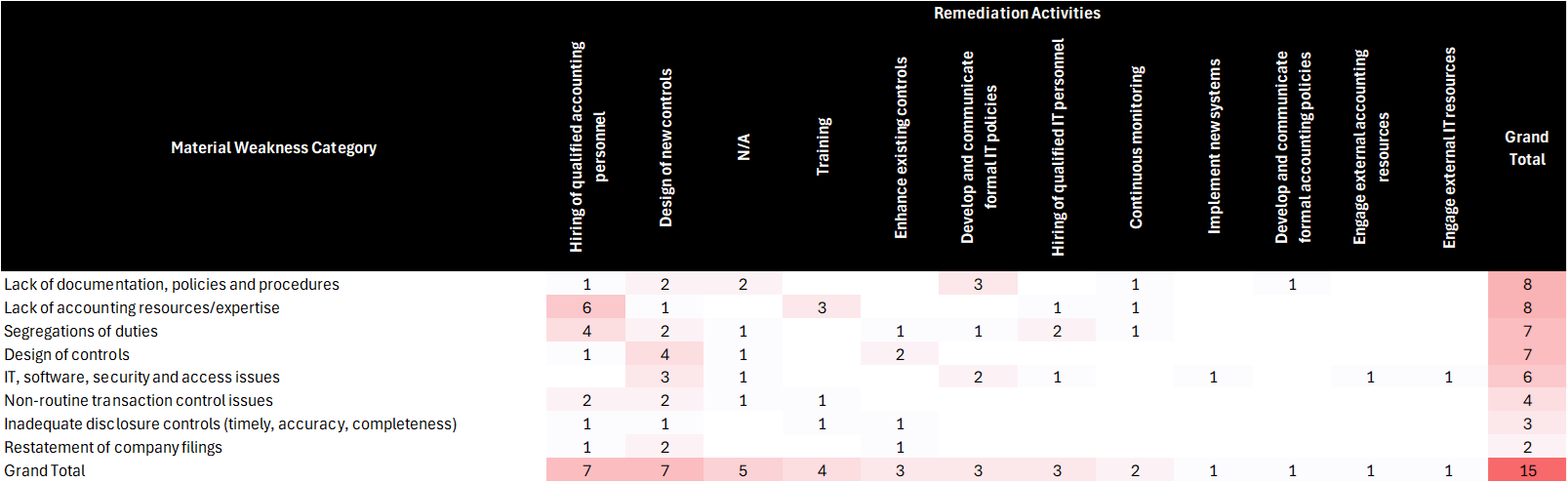
Below is the summary of MWs identified by category and functional area. Each cell represents the number of distinct entities where MWs of the respective category were identified in the functional area presented. As such, the sum of values in rows and columns does not add up to the total.
Most of the MWs were primarily related to:
Insufficient accounting expertise due to the lack of personnel with expertise in the areas of financial reporting, technical accounting, and SOX.
Absent or insufficient formal policies and procedures (e.g. accounting manuals, IT policies, and closing procedures).
Due to the limited size of startup teams, the overall insufficiency of accounting resources was commonly identified as a reason for the improper segregation of duties.
IT controls over access and program changes. Access to systems and data is traditionally viewed as a critical aspect of internal controls necessary to prevent unauthorized changes to data. In the context of an entity that actively engages in blockchain activities, inappropriate access may compromise the security of private keys and result in the misappropriation of digital assets.
Internally and externally generated information. Missing or insufficient activities performed to validate the completeness and accuracy of the information produced by the entity (IPE) and complementary user entity controls (CUEC) for information acquired from service organizations.
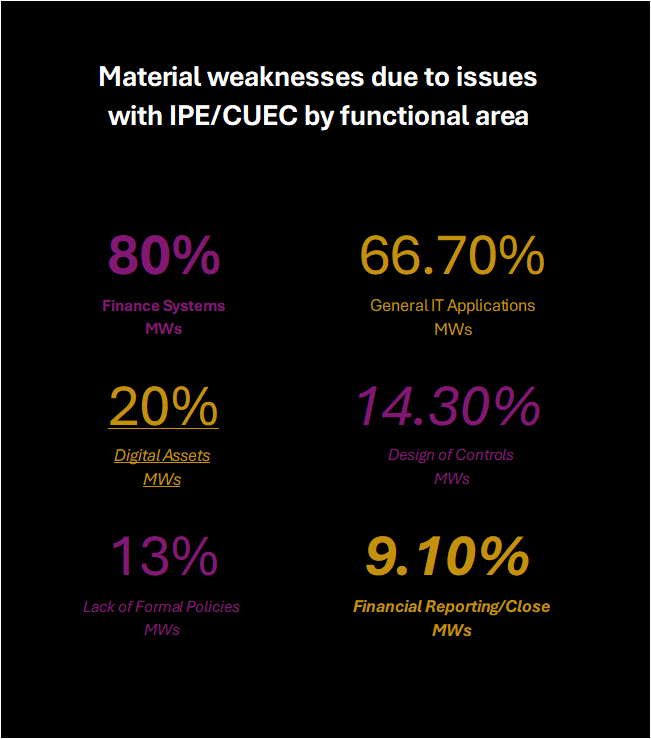
Deficient and absent controls over IPE/CUEC caused:
80% of material weaknesses in the area of accounting and finance systems and 66.7% in the area of general IT applications
20% of material weaknesses in the Digital assets area
14.3% of material weaknesses related to the Design of Controls
12.5% of material weaknesses are related to the Lack of documentation, control, and procedures
9.1% of material weaknesses in Financial reporting/close area
Remediation
The main types of remediation activities that companies described in their filings comprised of:
Hiring qualified accounting personnel and
Implementing new controls to address specific deficiencies identified.
Additionally, roughly 33% of issues identified did not have specific remediation activities stated. We summarized the types of remediation activities undertaken by the category of MWs:
We also wanted to share some practical advice on certain aspects of internal control that may be helpful for companies similar to those we studied and discussed above. We noted that several clarifications may be useful for our readers to improve their systems of internal control and address similar issues in the best possible manner.
1 - IT Controls
Thoughtfully assess and document the impact of IT systems on the business processes:
Establish a process of review and approval of each new blockchain network and the type of activity your business is engaged in this network.
Establish a process of review and approval before interaction with each new smart contract.
Implement controls specific to each network and smart contract design and functionality (properly consider the significance and materiality of each type of transaction for your business both individually and in aggregate).
Consider how the use of contract factories, proxies, and upgradable programs managed by third-party developers may affect your process of testing program changes for smart contracts.
Create and communicate to affected employees formal policies that address:
IT security
Management of private keys
Thoughtfully assess and document processes and controls over access privileges:
Only competent IT personnel with no conflicting responsibilities and duties should have access rights to make program changes.
Perform (and document) periodic reviews of user access and rights.
Be thoughtful about program changes. Track and be able to produce evidence over authorization and approval of development, testing, and implementation activities for all program changes and deployments.
2 - Management Review Controls
Avoid using management review control as a key control designed to address specific risks of material misstatement in the financial statements (e.g., Disclosure Committee Review Meeting to address the risk of omitted or incomplete footnote disclosures). Management reviews are a necessary part of monitoring activities but they frequently fail to ensure that specific types of misstatements were prevented or corrected. The better choice is to define process-level controls as simple activities that can be easily documented and verified. Examples of process-level control activities are:
Completed financial statements disclosure checklist,
Documented reconciliation between company books and blockchain records,
Tickmark as evidence of agreeing the price to Coinbase pricing file, and
Recalculation of the cost basis of crypto assets disposed.
Consider splitting all management reviews into smaller more digestible, testable, and robust process-level controls. Replace a single big review of revenue from Bitcoin mining with a thoughtful set of controls that involve minimum to no judgment. Choose those types of controls that can be fully or partially automated now or in the future. To do this we, first, need to determine all relevant data elements:
Plant. Say, we have one facility in the US and another and Australia, and in the revenue footnote in the financial statements we present revenue disaggregated by geographical regions. Then we would want to review revenue details by location (i.e. each plant).
Date. If we defined the contract term as limited to one day with daily renewals, then we would use different prices for bitcoin earned each day.
Bitcoin rewards and transaction fees earned. Bitcoin is received from the reward distribution address (when no pool is involved) or from the mining pool. When working with mining pool receipts, you would also need to verify that the amount you received is what has been earned, hence, you additionally will need to have all components of the payout calculations for your pool:
block subsidy
number of blocks mined
transaction fees
own hash rate
mining pool total hash rate
total network hash rate
network difficulty
mining pool fee rate
Daily opening (or other applicable) price of bitcoin.
Recorded amount of revenue for the period.
Now based on this list of data elements, the organization management need to create controls to ensure (with the appropriate level of precision) that:
Listed data is relevant, reliable, complete, and accurate.
Data is properly processed when used to measure dependent accounting objects or for other tasks that are relevant for the financial reporting.
Accounting records posted to capture processed data (when aggregated for the financial reporting presentation) provide a fair view on the company’s performance.
The following control procedures may be helpful for accounting teams responsible for mining revenue controls:
Reconciliation of the trial balance to the revenue detail report
Roll-forward of the crypto assets held
Reconciliation of prices used in crypto mining revenue detail to the historical prices from the principal market (e.g. the Company that always uses Coinbase to sell all bitcoin received should use Coinbase pricing)
Recalculation of the revenue based on details of bitcoin earned and principal market prices
3 - External Information
Keep in mind key considerations related to the use of service organizations:
Identify service organizations you use and ask them to share SOC reports with you (the fact that your vendor has a SOC report doesn’t help if the report states that all controls of a third party were deficient);
Review of SOC Reports to understand what third-party processes are, and controls in place, and be able to articulate the sufficiency of these controls to address risks relevant to your use of the third-party services. Do not forget to document your review.
If controls of a third party were not sufficient to address all relevant for your use case risks (e.g. no controls over the completeness and accuracy of reports that you use), implement missing controls necessary to address relevant risks.
Ensure that both the design and operation of controls (those controls that are relevant to your use case) are effective. When there is a deficiency noted or any of the relevant controls cannot reach its control objective, implement the controls necessary to achieve these objectives.
Remember to read through the “Complementary User Entity Controls” section of the SOC report. This section lists controls that need to be implemented and operated effectively in your company for you to be able to rely on any of the service organization controls listed in the report.
For information used in control activities, document your assessment of whether the information is relevant and reliable by considering the following:
Does this information describe recent observations or historical data? How are the object dynamics expected to affect the ability to use historical information to predict future behaviors of the object?
Does this information directly describe the specific object of accounting or the class of objects? If the latter, how broad is the class of objects that the information relates to?
Is the data sufficiently disaggregated to be useful at the required level of precision?
Whether the information is internal/endogenous (i.e. about your business) external/exogenous (i.e. about other businesses, a country in which your business operates, or anything else that extends beyond the boundaries of your business)
What is the level of expertise (credentials) of preparers?
Whether the process of acquiring the underlying data is simple & error-proof or complex & susceptible to errors?
Which parties participated in the origination, processing, and/or aggregation of this information?
Whether the information received is subject to regulatory oversight, and if so, what is the extent of this oversight?
Whether the information provided by a party with an effective governance that implemented robust controls over the preparation of this information?
Whether there is any external verification process for either the information itself or the effectiveness of controls over the preparation of this information?
Whether the source of information impose any restrictions and/or limitations on its use or disclaimers about its accuracy and completeness?
Terms and provisions of relevant contracts and policies?
Build a workflow for receiving, maintaining, and processing information received from service providers. This workflow should ensure that the information received:
Properly generated (i.e. use standard system reports with calculations and logic that cannot be modified; if you use reports with custom logic and calculations, ensure that any custom elements were reviewed and approved).
Clerically accurate and complete (i.e. that control totals add up correctly and agree to the source system and that individual items agree to the information you observe in the system interface).
Contains no unauthorized or improper changes (e.g. save the source file in a restricted storage space, make a copy for production use, and perform processing activities over the copy rather than the original document).
Finally, BYON (Bring Your Own Node) instead of using faulty and unreliable third-party block explorers. But even if you use data from your node, remember about general IT controls, and application level controls (in particular, controls over completeness and accuracy).
4 - Finance Policies
Assign the primary responsibility to formulate, disseminate, and update policies to an individual with the appropriate level of authority. Ensure that they are aware of the need to create policies in all key areas and emphasize the urgency and necessity of this.
Establish formal finance procedures and policies to address:
Related party transactions
Authorization of non-routine payment transactions
Period-end cut-off and accruals
Internal controls
Provide your accounting personnel with training opportunities that cover U.S. GAAP and financial reporting developments on cryptocurrency and other significant changes in accounting rules. This will facilitate timely updates to existing policies when necessary due to regulatory changes.
Finally, remember to perform a documented assessment of accounting conventions and policies that deviate from relevant GAAP requirements (non-GAAP policies) due to the materiality because with time the materiality of transactions may change.
5 - Continuous Improvement
Research the variety of sources available on topics of internal controls and evaluate the need to implement new best practices as you discover them. One example of what can be done is to consider the knowledge you may derive from your communications with auditors. Mimicking the work performed by external auditors is one of the good strategies that companies follow when designing an effective system of internal controls. To successfully implement this strategy, the management team needs to know what procedures auditors perform. One way to find out is to read through the critical audit matters (CAMs) section of the audit opinion, which identifies all significant procedures performed by auditors to gain comfort with the critical matter they identified. You can find the list of CAMs for Bitcoin mining companies in my previous post here or the summarized version below:
External Confirmation with:
Exchanges
Custodians of assets
Mining pools
Documentation of the Understanding and/or Evaluation of:
Regulatory environment (what are your rights and obligations based on)
Mining pool contracts (what you agreed to do, your rights and obligations)
Business process documentation (how you do what you agreed to do)
Accounting policies (how you record this)
Valuation methodology (how you measure this)
Footnote disclosures (how you present this)
Reperformance and/or Inspection:
Payout calculations
Realized gains/losses calculations
Impairment calculations
Reconciliations:
Book2Blockchain
Blockchain2Cash
IT Controls:
Security controls and management of private keys
Management of program/system changes (identification, testing, authorization, implementation)
Access (physical and application):
Provisioning of access (for new hires and changes in the function and/or level of authority)
Removal of access (for terminated employees and consultants as well as for internal movements to positions with different access levels)
Privileged access
Periodic access reviews
Service organizations:
Review SOC reports and bridge letters for periods from the date of the most recent SOC report available
Identify whether all relevant user entity risks are addressed by controls covered by the audit of the service organization that is being relied on
Identify any deficiencies noted by the auditor of a service organization
Implement complementary user entity controls to rely only on those internal controls of the service organization that were found to be effective by the auditor of the service organization during the relevant period
Observation:
Mining site visits
Miner equipment inventory count
Testing of significant assumptions and data elements:
Verify prices used to (re-)measure crypto mining revenue, and digital assets
Verify inputs of payout calculations
Test the reasonableness of assumptions used in the impairment analysis.
We may be able to use this list of audit procedures as the basis for some of the controls we design to address some typical risks of crypto mining businesses.
We did not access the dataset used by KPMG in the 2023 study of material weaknesses to validate that each of the 15 entities with MWs we identified was included in 242 MWs identified by KPMG. But we hope so.
From “Blockchain and Internal control - The COSO Perspective” which is available here. After consideration of this point of view, we realized that it is likely that none of the companies from our survey of bitcoin miners performed testing of controls over program changes in bitcoin core software, although this system does have a significant impact on the financial reporting of each of the bitcoin miners we studied. How did auditors of these companies consider this in performing these audits? Unfortunately, we cannot answer this question at this point.